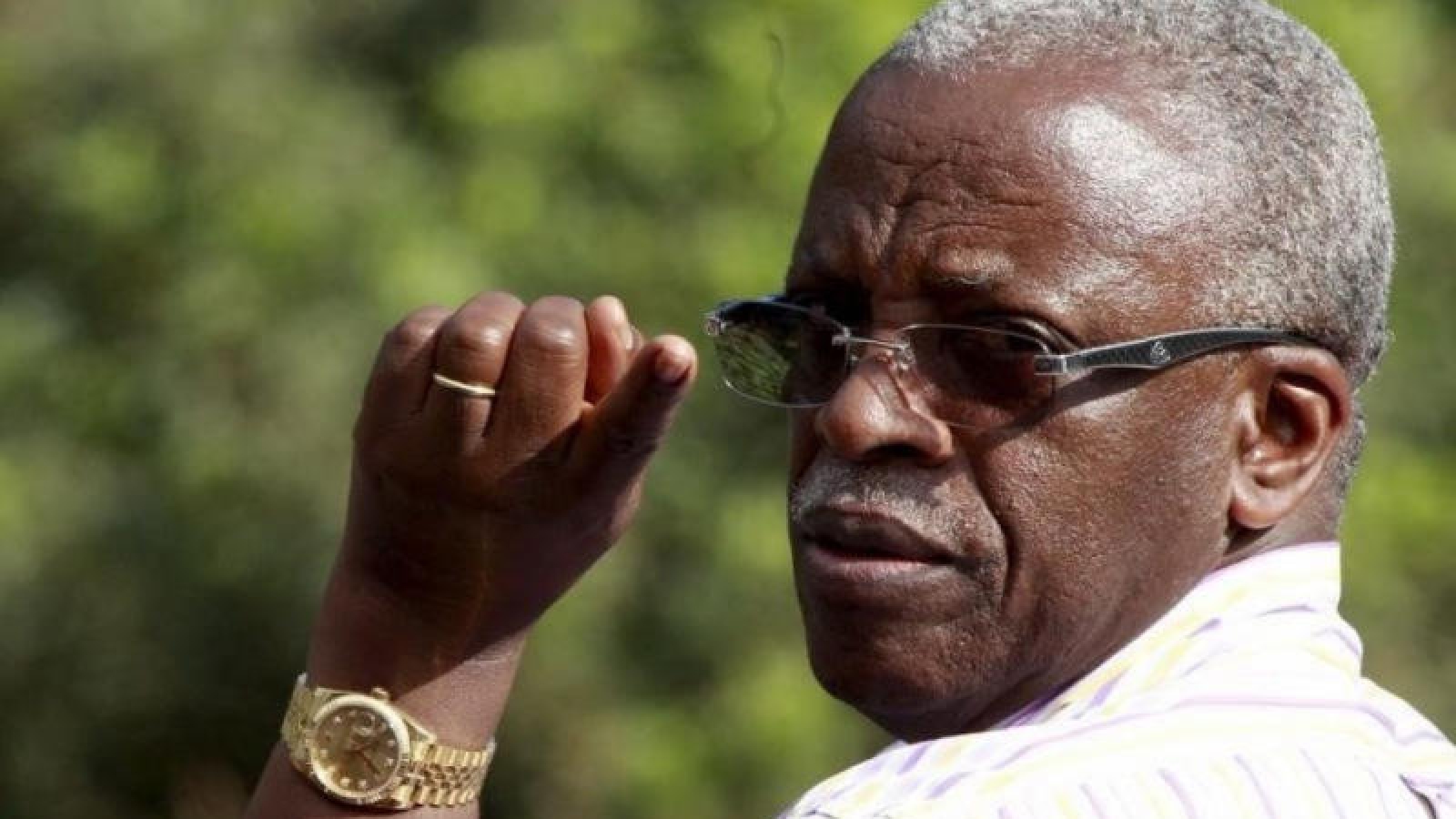
After Uganda’s 2016 Presidential election, one of the former presidential candidates, Mr John Patrick Amama Mbabazi, made preparations to challenge the election results in the Supreme Court. The offices of his lawyers were however broken into in the night leading to the 9th of March 2016. Evidence for the petition was taken in documents and computer equipment. This incident obviously negatively affected the petition. There are conflicting opinions on the motive for the burglary and who the perpetrators of the burglary were.
The incident though highlights the need to secure information in any organisation. Information could be destroyed or stolen for various reasons; to destroy evidence, frustrate litigation, identify the source of a sensitive or embarrassing news story, steal trade secrets such as business process, formula, recipe or outsmart a competitor in a bid process. Information loss most commonly occurs in Uganda as common theft of laptops, tablets, phones for resale on the 2nd hand electronics market. All these scenarios represent a huge cost to an organisation. It is therefore very important that the information is secured or at the very least, a copy of the information is maintained.
A number of options are available to prevent or mitigate the effect of such an event.
- The first line of defence is to physically secure the information. Critical documents need to be locked up in safes and filing cabinets. The same can be done for storage media such as flash drives, external disks, and mobile devices. That may not be adequate in the event of a break-in or a disaster such as a fire or a flood.
- The most sensitive of such documents could be kept in the custody of for example a bank or an agency that provides such specialised secure storage services.
- Copies of documents could be made as photocopies or scanned images of the documents which could, just like all other digital information, be backed up and kept off-site on storage media.
- Another alternative is to keep such information on the cloud; the cloud meaning an online service for storing and accessing data such as Google Drive (https://www.google.com/drive/), Dropbox (https://www.dropbox.com/), MEGAsync (https://mega.nz) , Microsoft OneDrive (https://onedrive.live.com/), etc. This, of course, requires that the organisation has a fast and reliable internet connection. The cost of online storage is quite cheap today. Some of the services offer free storage for 2 GB to 15 GB for Dropbox and Google Drive respectively. All these have paid services including Amazon Cloud Storage which charges USD 60 (UGX 210,000) per year for unlimited storage space.
In some cases, there’s sensitive information that the organisation will not want external parties to have access to, for example, confidential client/customer information, a special recipe, financial information, etc. Such information needs to be stored on secure media such as encrypted disks and computers. These should be inaccessible even if the villain has physical access to the medium.
A combination of boot/BIOS passwords and encryption need to be used. The boot password will stop unauthorised persons from booting (starting-up) the computer/device to access the information on the computer or mobile device.
Encrypting the disk on which the information is kept will scramble the data in the manner that the villain will not be able to read and make sense of it. There are also software solutions such as Prey (https://preyproject.com) and LoJack (http://www.absolute.com/en-GB/lojackforlaptops/home) that allow remote wipeout of information from stolen devices such as laptops and other mobile devices like phones and tablets.
Shortly after the Supreme Courts’ ruling on the petition, Mr Mbabazi cited the break into his lawyers’ offices among some of the reasons his team was not able to present ample evidence for his petition. This goes to underline the importance of organisations securing their information.
Contributed by
Dominic Kibuga
Digital Security Expert